DNS History Reveals Whether an Expired Domain Is Gold or Poison

A WHOIS record tells you who owned a domain. The DNS history tells you what they actually did with it. Every A-record swap, nameserver migration, and MX flip leaves a fingerprint in passive-DNS archives, and that paper trail is where you find out whether the expired domain in your cart is a sleeper asset or a poisoned well. This guide walks the DNS-forensic workflow I use before any expired-domain buy: which records matter, the patterns that flag a spam tenant, and how to read a five-year DNS timeline fast enough to make a buy decision before the auction closes. Or walk before you bid, which is usually the right move.
What DNS History Actually Shows (And Why It Matters)
DNS records function as a domain’s operational fingerprint, revealing who hosted it, where traffic flowed, and how email was configured. WHOIS tells you the registrant on paper, DNS tells you what infrastructure that registrant actually wired up. In my experience, the gap between the two is where most of the interesting findings live. Well, almost all of them. The rest live in the Wayback snapshots, which is a separate conversation.
Quick vocabulary
- A record
- The DNS entry that maps a domain to an IPv4 address. Tracks which physical host (and which neighborhood of IPs) served the site at a given point in time.
- NS record
- The nameserver pair (or larger set) that authoritatively answers queries for the domain. Changes here usually mean a registrar, hosting, or DNS-provider switch.
- MX record
- The mail-exchange route. Tells you who handled email for the domain, Google Workspace, ProtonMail, a bulk-sender like SendGrid, or something less polite.
- TTL
- Time-to-live, in seconds. Low TTLs (60, 300) signal a domain ready to flip infrastructure quickly, common in failover setups but also in fast-flux spam operations.
- Dangling DNS
- An A or CNAME record pointing to an IP or hostname the owner no longer controls. Sometimes harmless residue, sometimes a takeover vector someone is actively exploiting.
- Parking provider
- A nameserver or A-record cluster operated by Sedo, GoDaddy, Bodis, or similar, used to monetize unused domains with ad pages. Long parking tenure is a “never developed” signal.

The DNS Footprint: IPs, Name Servers, and Mail Records
A records map domain names to IP addresses, historical A records show previous hosting providers, server locations, and infrastructure changes that may signal past use as a spam operation or link farm. NS (name server) records identify which DNS provider managed the domain. Frequent NS switches can indicate ownership turnover, technical instability, or in the worst cases the kind of rotation pattern fast-flux botnets use to dodge takedowns. MX (mail exchange) records expose email routing history, domains previously configured with bulk-mail services or disposable email providers often carry reputational baggage that follows the domain even after the MX entry is gone.
Together, these records create a timeline of technical decisions. For expired domain hunters, sudden IP migrations to known spam networks or MX records pointing to blacklisted mail servers are immediate red flags requiring deeper investigation before acquisition. (I had a client last quarter pull the trigger on a DR 42 domain that looked perfect on Ahrefs, the DNS history showed the MX record had pointed to a known bulletproof-host mail server for eighteen months in 2021. We walked.)
How Historical DNS Data Gets Captured and Stored
DNS history services operate by periodically querying and archiving domain nameserver records, A records, MX records, and other DNS entries as they change. Most providers crawl the DNS infrastructure at intervals ranging from daily to weekly, building a timeline of configuration snapshots. When a domain switches hosting providers, email services, or ownership, these changes leave traces in the DNS layer that get logged and indexed. (One audit last spring, the crawl frequency was the whole story: the candidate had flipped NS twice in a week between two scheduled SecurityTrails passes, and we only caught it because Viewdns happened to pick up the intermediate state. Lucky catch, frankly.)
WHOIS tells you the registrant on paper. DNS tells you what infrastructure that registrant actually wired up.
The lookback window varies considerably by service. Free tools typically offer 1-3 years of historical data, while commercial platforms may archive records stretching back 5-10 years or more. Coverage depends on when the service first began monitoring a particular domain and how frequently it captured updates. For expired domain vetting, deeper history reveals more potential red flags like frequent IP migrations, spam-associated mail servers, or suspicious nameserver patterns that suggest prior misuse.
Pro tip
Look at the TTL values across the timeline, not just the records themselves. A domain that ran 86400-second (24-hour) TTLs for years then dropped to 60-second TTLs right before an ownership change is announcing that whoever has it next plans to flip infrastructure fast. Stable TTLs are a stability signal in their own right.
Red Flags Hidden in DNS Records
Frequent IP or Name Server Changes
Frequent IP or name server switches signal instability, often the fingerprint of spam networks, hosting churn, or domains cycling through multiple owners. A clean domain typically maintains consistent infrastructure for months or years. Rapid changes within weeks suggest the domain may have served disposable content or been repeatedly penalized and abandoned. Or both, honestly. The two failure modes love each other’s company.
Same six signals tell two very different stories depending on the pattern they form:
| Signal | Clean DNS history | Poisoned DNS history |
|---|---|---|
| NS stability | One or two nameserver changes across the domain’s life, each tied to a real hosting migration | Five or more NS changes in twelve months, especially across budget hosts or parking services |
| A-record neighborhood | IPs on reputable shared hosts, managed providers, or dedicated infrastructure (AWS, WP Engine, Cloudflare) | IPs on known bulletproof hosts, blacklisted ranges, or clustered with PBN-flagged neighbors |
| MX history | Google Workspace, Microsoft 365, or a single business mail provider held for years | Bulk senders, disposable-mail services, or blank MX during long stretches of supposed operation |
| Parking tenure | Brief parking windows tied to ownership transitions | Multi-year parking on Sedo, Bodis, or GoDaddy nameservers, the “never developed” tell |
| TTL behavior | Steady 3600-86400 second TTLs, occasional drops for planned migrations | Aggressive 60-300 second TTLs sustained across months, classic fast-flux infrastructure |
| Cross-signal alignment | WHOIS transfers and DNS shifts spaced months apart, organic timing | WHOIS transfer and full DNS overhaul within days, classic flip pattern |
Check DNS timelines for patterns: two or three migrations during natural business changes are normal, but five-plus shifts in a year raise red flags. Cross-reference these changes with WHOIS transfer dates and historical content snapshots to spot domains used for link farms, affiliate churn, or black-hat SEO tactics. Three changes in six months while the MX record pivots from Google Workspace to a bulk sender. That’s a profile, not a coincidence. (Saw this exact pattern on a DR 38 candidate in March, the MX flip to Mailgun was the tell that flipped the verdict from “maybe” to “absolutely not.” Backed off the bid that afternoon.)
Known Bad Neighborhoods: IPs Tied to Spam or Malware
Once you’ve mapped historical IPs, cross-reference them against reputation databases to uncover spam, malware hosting, or botnet activity. This step is critical when building PBN domains, since penalized IPs can taint clean content even after a hosting move.
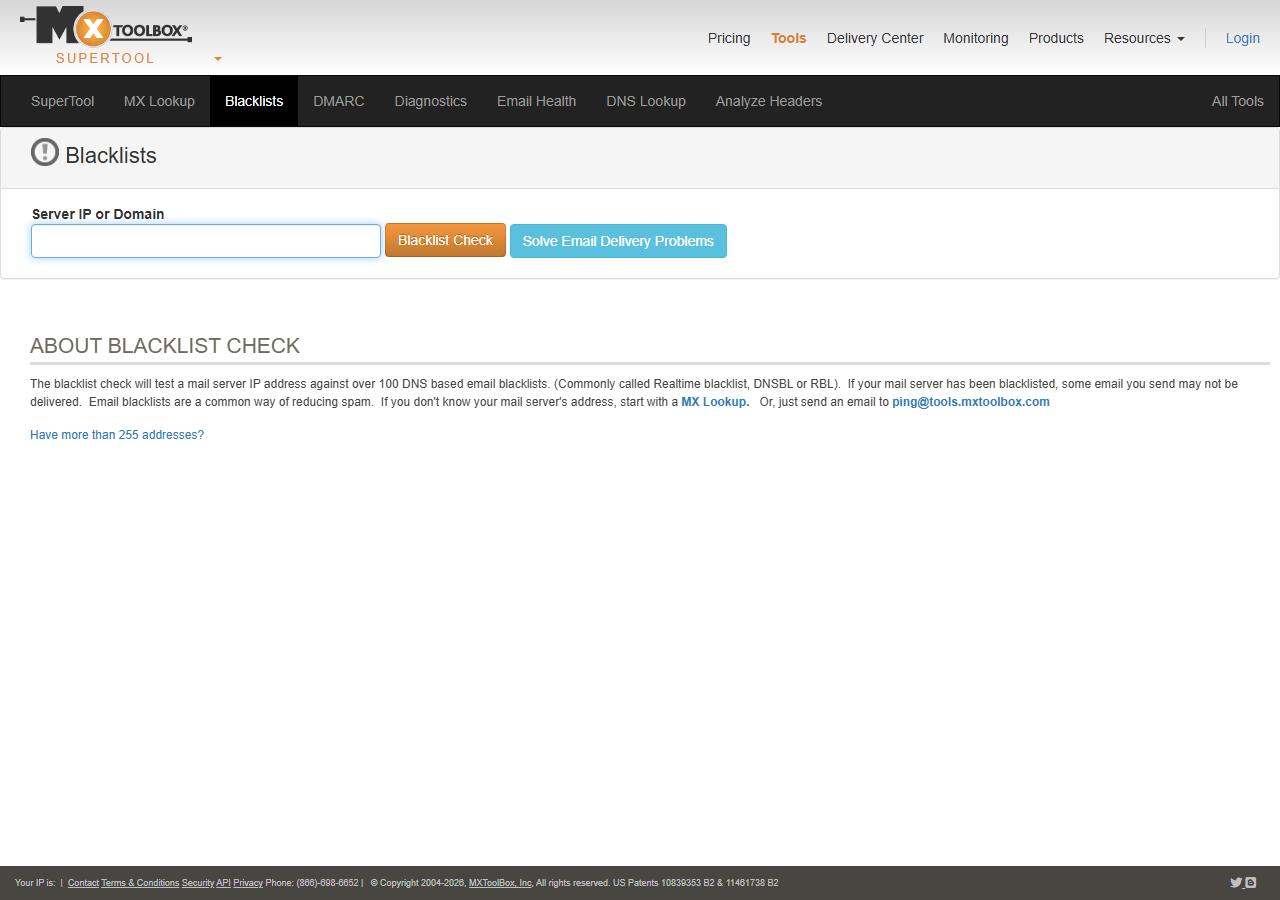
Start with Spamhaus (spamhaus.org/lookup) to check if an IP appears on DNS blacklists, queries are free and reveal current or historical spam designation. MXToolbox Blacklist Check (mxtoolbox.com/blacklists.aspx) scans 100+ blacklists simultaneously and flags reputation issues that may linger even after DNS changes.
For researchers digging deeper, IPVoid (ipvoid.com) aggregates 90+ blocklist databases and shows malware distribution history. Cisco Talos Intelligence (talosintelligence.com) adds context with threat scores and historical security events tied to specific IPs.
Compare multiple snapshots across your DNS timeline, if an IP was blacklisted during the domain’s tenure, assume search engines noticed. (Honestly, this is the check that’s saved me from the most regrettable buys. Twice in the last year a domain that scored clean on Ahrefs lit up Spamhaus when I pulled the historical A record from 2019.)
Parking Pages and Ad Networks in the DNS Trail
A domain parked on GoDaddy’s or Sedo’s ad servers for years signals it was never developed, usually harmless but a flag that any backlinks came from non-editorial sources. More troubling: IP addresses tied to low-quality redirect farms or networks known for spammy link schemes. Cross-reference resolved IPs with blacklists and spam databases, if the domain bounced between multiple parking services in short bursts, it may have been flipped by domainers who built toxic link patterns to inflate resale value.
Note
Parking on its own isn’t disqualifying, plenty of legitimate domains sit parked between owners. But parking combined with NS rotation, blacklisted A-record history, or a sudden MX change to a bulk sender is the pattern that flips the verdict. Read the cluster, not the data point.
Parking isn’t disqualifying, but frequent host changes combined with link-builder fingerprints warrant deeper scrutiny. For most teams, the cleanest rule of thumb is this: long single-provider parking is mostly fine, short rotational parking across three or four providers is almost never fine. Mostly. Edge cases exist, but they’re rare enough to round off.
Combining DNS and WHOIS History for Full Context
Matching Ownership Changes to DNS Shifts
Cross-referencing WHOIS registrant data with DNS timeline shifts reveals whether a domain changed hands and immediately swapped infrastructure, a hallmark of flipping or spam recycling. Pull historical WHOIS snapshots from services like DomainTools or WHOIS History and align ownership transfer dates with DNS record changes in your DNS history tool.
If registrant details flip and nameservers or A records update within days, you’re likely seeing resale activity rather than organic ownership. Bulk patterns matter too, domains sharing identical nameserver sequences across multiple registrant changes suggest portfolio churn or automated PBN assembly. For researchers vetting expired domains, mismatched timing is a yellow flag, legitimate sites rarely overhaul DNS immediately after acquisition unless the buyer plans rapid repurposing.
The DNS audit cycle
Registration Gaps and Expiration Patterns
When a domain expires or changes ownership, WHOIS records shift, often creating brief windows of vulnerability. Cross-referencing expiration dates with DNS history reveals whether a domain lapsed into parking pages, went offline entirely, or was snapped up by resellers who may have altered its content before putting it back on the market. Gaps between registration periods paired with DNS downtime can indicate abandonment, automated squatting, or ownership disputes, all warning signs for buyers.
Look for registration churn. Domains that flipped between registrants multiple times in short succession often carry baggage from prior uses. Compare WHOIS snapshots against DNS record timestamps to spot intervals where no legitimate site was active. These dormant periods may coincide with spam campaigns, redirects to affiliate networks, or link farm tactics that accumulated penalties. Tools that merge WHOIS timeline data with DNS snapshots let you trace exactly when a domain lost its original purpose and what replaced it. For full context on the WHOIS side of this pairing, see our companion piece on historical WHOIS records, the two workflows are sister pieces of the same forensic discipline.
Tools and Methods for Checking DNS History
Free Lookup Services and APIs
Several free tools let you peek into a domain’s DNS past without opening your wallet. Similarweb’s traffic and infrastructure overview can corroborate hosting changes from the demand side, but for raw DNS records SecurityTrails offers limited free lookups showing historical A, MX, and NS records, useful for spotting past hosting providers or mail server changes. DNSHistory.org archives DNS snapshots dating back years, revealing when nameservers switched or subdomains appeared. Viewdns.info’s DNS record history tool pulls archived data quickly, ideal for fast red-flag checks before bidding on expired domains.
For technical operators, Screaming Frog’s log-file analyser plus a custom dig wrapper can produce a usable internal DNS timeline if you’ve been monitoring the domain yourself, less common on expired-domain workflows, more common on competitor-audit work.
These services surface ownership transitions and hosting migrations that might indicate spam history or previous penalties. Most free tiers limit query volume or historical depth, so combine multiple sources for fuller coverage. I’d argue the free tier of SecurityTrails plus a paid MXToolbox subscription covers 80% of expired-domain triage at minimal cost. Maybe 75. Depends on how often the candidates you’re vetting fall outside the major hosting providers, which is a regional thing more than anything else.
Enterprise Platforms for Bulk Domain Vetting
For teams vetting hundreds of expired domains monthly, manual checks quickly become impractical. Enterprise platforms like DomainTools, Spamhaus Domain Block List (DBL), and SURBL aggregate DNS history, IP reputation scores, malware associations, and historical WHOIS data into single dashboards with automated risk ratings. These services query decades of passive DNS records, flag domains previously tied to phishing campaigns or spam networks, and surface ownership patterns that suggest past abuse.
Bulk API access and pre-computed trust scores let you disqualify toxic domains in seconds rather than hours, the kind of throughput that turns DNS forensics from a “we’ll check the top three” exercise into a routine first-pass filter. SEO agencies, domain brokers, and security teams managing large portfolios typically need this depth and can justify the subscription cost (typically $500-$5,000 annually).
When free tools show conflicting signals or you’re investing significant capital in aged domains, paid platforms provide the forensic depth and liability coverage manual research cannot match. They also archive snapshots that public tools prune after months, preserving evidence of short-lived malicious campaigns that would otherwise vanish from the public record before you could read them.
Making the Call: When DNS History Says Buy or Walk Away
Look, DNS history doesn’t lie, but it does require interpretation. A stable nameserver record over years, especially tied to a single registrar and hosting provider, suggests consistent ownership and purpose. That’s a green light. Probably. Multiple rapid NS changes, particularly across budget hosts or parking services, signal speculation, abandonment, or worse: automated churn typical of spam networks.
Start with continuity. If DNS records show the domain pointed to legitimate hosting (verified via reverse IP lookups) for at least two years before expiration, and WHOIS ownership remained consistent, you’re likely safe. Match this against Wayback Machine snapshots to confirm real content existed during that period. (For most teams, this is the single highest-yield check you can run in under ten minutes.)

Red flags include nameserver hops every few months, especially to known PBN infrastructure or registrars favored by link spammers. A domain that cycled through five hosts in eighteen months probably changed hands repeatedly or served disposable content, neither scenario builds authority worth paying for. Truth is, the worst expired domains aren’t the obvious spam, they’re the ones with one clean WHOIS owner on paper and a DNS timeline that tells a completely different story underneath.
A domain parked on Sedo nameservers for three years, then briefly active on cheap shared hosting, then expired? Walk away. Don’t even open the auction tab. A domain on stable AWS or WP Engine infrastructure for four years with gradual traffic decline? Strong candidate. The kind of profile you actually want to bid on, when you can find one.
✓
Worth investigating
- ›Two or more years on one nameserver pair
- ›A-record IPs that pass MXToolbox and Spamhaus
- ›MX history tied to a single business mail provider
- ›Parking only at expiration, not throughout the timeline
- ›WHOIS transfers spaced months apart from DNS shifts
×
Skip without looking back
- ›Five or more nameserver changes in twelve months
- ›Any A-record IP flagged by Spamhaus during the domain’s tenure
- ›MX records pointing to bulk senders or disposable mail services
- ›Sustained 60-300 second TTLs across multiple months
- ›WHOIS transfer plus full DNS overhaul inside a single week
The goal isn’t perfection, it’s avoiding domain penalties by filtering out manufactured histories. Cross-reference DNS stability with backlink quality and content archives. When signals align, buy. When they contradict, pass. DNS history vetting isn’t optional when budget, authority, and strategy are on the line, a domain’s past directly shapes its present value, and ignoring spam penalties, toxic backlink profiles, or ownership churn can derail link-building campaigns and waste resources on metrics that look strong but deliver nothing. When vetting domains for SEO, treat DNS records as forensic evidence: they reveal whether a domain was parked, penalized, or pivoted through sketchy niches.
Try it this week
Pick three expired domains on your shortlist. Pull their DNS timelines before you bid.
-
1
Run each domain through SecurityTrails (free tier). Export A, NS, and MX history for the full lookback window. -
2
Drop every historical A-record IP into MXToolbox and Spamhaus. Mark any IP that lit up during the domain’s tenure. -
3
Overlay WHOIS transfer dates and Wayback snapshots. Any domain with DNS, WHOIS, and content all shifting in the same week drops off the shortlist.
The domains that survive this filter are worth real budget. The ones that don’t survive cost you nothing except the bid you didn’t place.
Related guides
- Historical WHOIS Records, The companion forensic discipline, ownership history paired with DNS history is the full picture.
- Spotting Expired Domains, The discovery pipeline that surfaces topic-relevant candidates before they hit the auction shortlist.
- Blacklist and Penalty Checks, The pre-purchase blacklist workflow that pairs with DNS-history vetting.

