
Threat Intelligence Automation That Actually Maps Attacker Tactics
Threat intelligence automation transforms raw attack indicators into mapped adversary behaviors, allowing security teams to anticipate tactics rather than chase...


GSA, RankerX, Money Robot, scraping, automation scripts, footprint removal, indexer services, spam techniques that still work. The stuff others won’t publish.
9 articles

Threat intelligence automation transforms raw attack indicators into mapped adversary behaviors, allowing security teams to anticipate tactics rather than chase...

Linux dominates digital forensics because it offers transparent, scriptable access to raw disk data without altering evidence—a non-negotiable requirement when...

AI-powered automation transforms business operations by deploying machine learning models to handle repetitive tasks, make data-driven decisions, and scale processes...

CAPTCHA systems stand as digital gatekeepers, designed to separate human visitors from automated bots—but captcha bots now solve these puzzles...
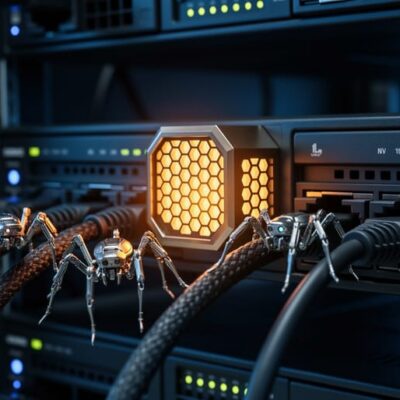
Deploy simulated services that mimic real infrastructure—vulnerable WordPress endpoints, exposed admin panels, or link submission APIs—but log every probe without...

Borrow threat models from DefCon and Black Hat conferences to mask automated link building operations. Treat search engine crawlers as...

Gray-hat hacking occupies the contested boundary between security research and exploitation—techniques that reveal vulnerabilities without malicious intent but often without...

A honeypot is a decoy system that attracts attackers to reveal their methods—particularly effective against automated black hat attacks targeting...

Black-hat hackers weaponize technical skill for theft, sabotage, and unauthorized access—driven by financial gain, ideology, or disruption rather than ethical...