Why Your Proxy Fleet’s G Suite Credentials Are Already Compromised (And How to Fix It)

Rotate G Suite service account keys every 90 days maximum using a CI/CD pipeline that programmatically generates new credentials, updates secret stores (Vault, AWS Secrets Manager), and revokes old keys—automating the most common credential leak vector in proxy fleets. Restrict OAuth scopes to the minimum required permissions per service account; a proxy authentication service needs only Directory API read access, not full domain delegation. Enable domain-wide delegation only when absolutely necessary, then monitor Admin SDK audit logs for anomalous API calls—unusual geographic locations, sudden spike in directory queries, or off-hours access patterns signal compromised credentials. Implement IP allowlisting at the workspace level for service accounts that authenticate proxy infrastructure, combined with user agent fingerprinting to catch credential reuse outside your controlled infrastructure. Deploy Cloud Identity-Aware Proxy or equivalent zero-trust controls between your proxy fleet and G Suite APIs to enforce certificate-based authentication alongside service account credentials, eliminating bearer token theft as a single point of failure.
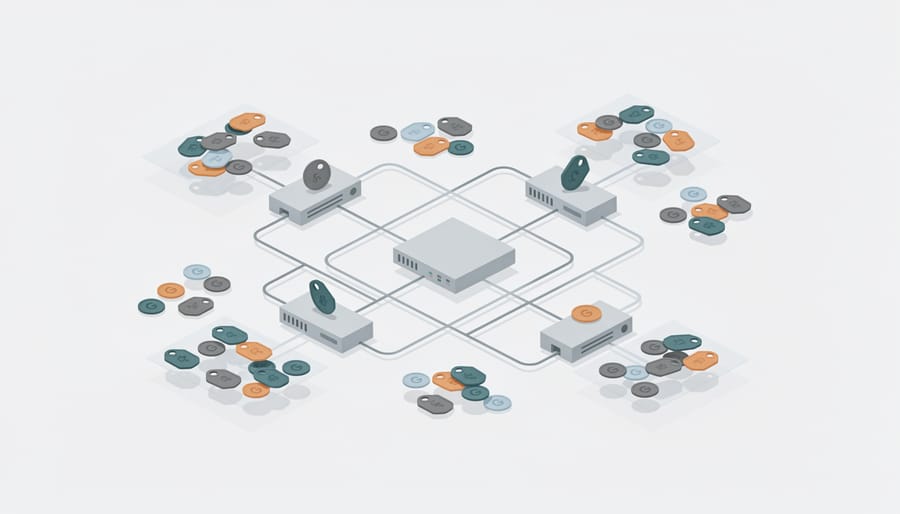
The Credential Sprawl Problem in Proxy Operations
Where G Suite Secrets Hide in Your Infrastructure
G Suite credentials scatter across your infrastructure in predictable patterns. Deployment scripts often hardcode service account keys for automation tasks—check Terraform state files, Ansible playbooks, and shell scripts in version control. Docker images frequently bake credentials into environment variables or configuration layers; run image scans to detect JSON key files embedded during builds. CI/CD pipelines store G Suite tokens as pipeline secrets or environment variables in Jenkins, GitLab CI, or GitHub Actions—audit who can view and modify these values.
Shared Google Drives pose overlooked risks: developers frequently store service account keys in “team folders” with overly permissive sharing settings. For teams managing proxy fleet security, operator workstations become attack vectors—credentials cached in browser storage, saved in local config files, or logged in command histories. Configuration management tools like Chef cookbooks and Puppet manifests commonly contain authentication tokens in plaintext attributes.
Why this matters: Each exposure point creates lateral movement opportunities for attackers. A single compromised deployment script can grant domain-wide delegation access across your entire G Suite tenant.
For: DevOps engineers, security architects, infrastructure operators managing authentication at scale who need to map where credentials actually live before implementing rotation strategies.
G Suite-Specific Security Controls That Actually Matter
Service Account Architecture for Automated Proxy Management
Service accounts powering proxy fleets require strict isolation to prevent credential compromise from cascading across your infrastructure. Start by creating dedicated service accounts per function—one for authentication refresh, another for user provisioning, a third for logging—rather than a single god-mode account. Each should request only the OAuth scopes it needs; an account refreshing access tokens doesn’t need domain-wide delegation for user creation.
Rotate keys programmatically every 30-90 days using Cloud Scheduler or cron jobs that generate new keys, update your secret manager (Google Secret Manager, HashiCorp Vault), verify the new key works, then revoke the old one. Store the rotation timestamp and key ID as metadata so you can audit key age across your fleet. Never embed keys in code or environment variables; fetch them at runtime from your secret manager with short-lived leases.
Isolate blast radius by binding each service account to the smallest possible scope of resources. Use Workspace domain delegation sparingly—if a service account only manages users in a specific organizational unit, restrict its delegation accordingly. Enable API access logging in Cloud Logging to track every call each service account makes; unusual patterns like geographic anomalies or privilege escalation attempts should trigger immediate key rotation and forensic review.
Tag service accounts with owner information, rotation schedules, and purpose labels so incident responders can quickly identify dependencies when credentials leak. Monitor for concurrent usage from multiple IP addresses—a strong indicator of credential theft. Test your rotation pipeline quarterly under load to ensure it won’t cause service disruption during an emergency revocation.
OAuth Token Lifecycle in High-Volume Environments
OAuth tokens typically expire within 60 minutes, creating a refresh challenge when hundreds of proxy nodes authenticate simultaneously. Naive implementations trigger G Suite’s rate limits (currently 10 requests per second per user) and generate avalanche-style security alerts that mask genuine threats.
Stagger refresh windows across your fleet using token TTL plus random jitter (15-45 seconds). This spreads the load and prevents synchronized bursts. Implement a centralized token service rather than per-node refresh logic—a single Redis instance can coordinate token distribution across 500+ nodes while staying well under API quotas.
Monitor refresh failures separately from initial auth failures. A spike in refresh denials often indicates IP reputation issues or leaked credentials being rotated by Google. Set alerts when refresh error rates exceed 2% over five minutes.
For graceful revocation, maintain a deny-list with 90-second propagation SLA. When revoking compromised tokens, immediately block at your authorization middleware layer before the Google API call completes—this prevents the 200-400ms window where revoked tokens might still authenticate locally.
Cache token metadata (scopes, expiry, associated service account) alongside the token itself. This enables quick scope validation without additional API calls and helps debug permission errors without exposing the actual token value in logs.

Secrets Management Patterns for Proxy Fleet G Suite Integration
Dynamic Secret Injection Without Hardcoding
Preventing credential leaks starts with eliminating secrets from configuration files entirely. Runtime injection delivers G Suite credentials to proxy nodes only when needed, reducing exposure windows and simplifying rotation.
Agent-based retrieval using HashiCorp Vault or AWS Secrets Manager works well for distributed fleets. Configure each proxy node to authenticate via instance identity, then pull credentials on startup. Example using Vault Agent:
vault agent -config=/etc/vault/agent.hcl
The agent template writes credentials to a local socket, which your proxy reads without ever touching disk. Rotate the secret in Vault, restart the agent, and every node picks up the new value within seconds.
Sidecar patterns suit Kubernetes deployments. A dedicated container fetches secrets and exposes them via shared volume or environment variables. The external-secrets operator syncs from cloud providers automatically, triggering rolling updates when credentials change.
Init containers handle one-time injection before the main proxy starts. This snippet fetches a service account key at pod launch:
initContainers:
– name: fetch-creds
image: google/cloud-sdk:slim
command: [“/bin/sh”, “-c”]
args: [“gcloud secrets versions access latest –secret=gsuite-key > /secrets/key.json”]
volumeMounts:
– name: secrets
mountPath: /secrets
Mount the volume read-only in your proxy container. The credential exists in memory only, never persisted to the image or config map.
Detection and Response When G Suite Access Goes Wrong
When G Suite credentials power infrastructure at scale, you need detection that fires before damage spreads. Start with Google Workspace’s alert center to flag anomalous API usage—sudden spikes in Drive exports, Calendar shares to external domains, or Admin SDK calls from unexpected IPs all signal potential compromise. Configure alerts for credential reuse patterns: the same OAuth token authenticating from multiple geolocations within minutes indicates session hijacking or leaked tokens circulating through attacker infrastructure.
OAuth grants deserve dedicated monitoring and audit logging. Watch for applications requesting broad scopes (gmail.readonly, drive.full) without business justification, especially those created recently or by unknown publishers. Google’s Token Access API lets you audit which third-party apps hold access; script regular reviews to revoke stale grants and identify shadow IT risks.
For operational visibility, pipe G Suite audit logs into your existing SIEM or log aggregation stack. The Reports API exposes login events, admin actions, and data access patterns as structured JSON. Focus on high-signal events: admin role grants, security setting changes, domain-wide delegation modifications, and authentication failures clustered by user or IP. Correlate these with your proxy fleet metrics to spot lateral movement—compromised accounts often probe internal resources immediately after initial access.
Build runbooks for common scenarios: revoke sessions via Admin SDK when detecting anomalies, automate temporary account suspension for repeat authentication failures, and trigger credential rotation workflows when logs show potential exposure. Detection without response procedures leaves teams scrambling during incidents.

Treating G Suite credentials as ephemeral, narrowly scoped secrets rather than static configuration values fundamentally shifts proxy fleet security from damage control to defensive architecture. Short-lived tokens, service account rotation, and continuous audit trails turn authentication into an observable, time-boxed process instead of a permanent vulnerability surface. This approach directly addresses the operational reality that credentials will eventually leak—what matters is limiting their blast radius and detection window. For DevOps teams running authentication at scale, this mental model converts G Suite security from a compliance checkbox into a structural advantage that compounds over time as infrastructure grows.

